An automatic dog feeder seemed like a good idea at the time. One of our team members had a COVID puppy, Mango, who ate constantly, and their kids had long abandoned the promises to help. All was good until a malfunction dumped a pound of dog food on Mango mid-feed. The “brave” puppy was too scared to eat from it again.
What does this have to do with cybersecurity? It illustrates the importance of automation and orchestration as they are pillars of proper cybersecurity architecture. But it highlights that there can also be unforeseen risks to consider.
Successful, secure digital transformation requires an automation and orchestration mindset. Humans are not capable of keeping pace with the amount of data, threats and the ever-increasing sophistication of attackers who are leveraging their own automation strategies. As one embarks on zero trust, this becomes even more critical. Automation and orchestration are foundational to the U.S. Cybersecurity and Infrastructure Security Agency’s (CISA) Zero Trust Maturity Model.
But what does automation and orchestration mean in the context of cybersecurity? We’ll start with some definitions. Automation refers to using technology to automatically perform tasks or actions that humans previously did manually. Orchestration, on the other hand, refers to integrating and coordinating different tools and technologies to create a unified security platform. In the case of the automatic pet feeder, automation would be dispensing food at scheduled times, while orchestration would be aligning feeding times with Mango’s dietary needs and ordering more food when supplies went low.
Automation and orchestration in a zero-trust architecture
How are these practices implemented? As suggested earlier, automation can simplify the enforcement of security policy. Take, for example, the manual process of application segmentation in the context of a zero-trust architecture. Zero trust is a security model that assumes that all users, devices and applications are untrusted and must be verified before granting access to resources and then only grants what is needed by the business — moving away from implicit trust, hence the term “zero trust.” Thus, moving to zero trust allows for granular application segmentation policies that grant access based on business policies.
This is powerful, but creating these rules manually can be difficult and time-consuming. The first step is having the visibility to be able to understand the landscape and what is happening in the environment to set up proper segmentation policies. This was discussed in more depth in this article.
But next comes the processes of creating, maintaining and enforcing the segmentation rules, which will rely heavily on automation techniques coupled with AI/ML insight to create recommendations based on actual usage. It could say, for example, that visibility shows that only the finance department accesses a critical financial software package, even though the entire company has access. It could then automate the creation of a segmentation rule thereby reducing the attack surface by removing unnecessary trust in the environment.
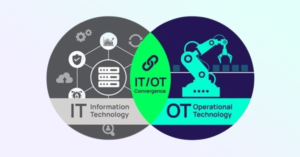
In a zero-trust world, the network stack and the network itself have been removed from the attack surface, leaving effectively the zero-trust platform (like an SSE architecture), the endpoint and identities as the reduced enterprise attack surface. This means that tools like SSE, EDRs and IDPs might each employ automation for efficiency but need orchestration among them.
Take, for example, the previous case where an automatically created segmentation policy only grants access to an application to the finance department. What if the EDR could spot risky behaviour from an employee in the finance department whose device also wasn’t up to security standards? Orchestration between the EDR and SSE would limit access (either a block, limited access or isolated browser access) to the important financial application. In a more radical example, deception could be brought into play with lures that a legitimate employee in finance would never find or use but an attacker might, and automation could immediately send a signal to the security operations team and also create a false application with false data for the attacker to access.
Automation allows for the quick and efficient deployment of security policies, essential for enforcing the zero-trust model. By automating the deployment of security policies, security teams can ensure that access is only granted to authorized users and devices. Orchestration enables security teams to automate workflows and processes across different security tools, allowing them to quickly and efficiently respond to security incidents. In Mango’s case, these techniques did provide her with food on time and reduced the burden on her owners.
Where things get complicated
So what are the challenges? Automation and orchestration are fine when it is done incrementally and strategically, but they can potentially be used by an attacker even when they don’t know the specific pages of the playbook or code of the automated scripts. With an intelligent opponent and given multiple opportunities to attack and learn from one another, automation that can be seen and triggered intentionally can be exploited. This is seen in the fraud world, where large volumes of fraudulent transactions give real-time feedback to cyber criminals: when something is effective, it is noted and used again immediately with swarm-like intensity.
There are three general principles to employ when using automation and orchestration to minimize these risks and maximize the gains in efficiency, cost reduction, and security effectiveness:
Overall, automation and orchestration are critical components of a strong cybersecurity strategy. Arguably, they may be necessary to grow in maturity and handle advanced threats at scale. But the real goal is business transformation: network, application, and security. This mentality will enable us to focus on that and get on with that transformation. Automation and orchestration are vital qualities of a large-scale zero-trust platform, and as we’ve seen, they have to be done in a way that minimizes the ability of adversaries to abuse and turn them on the defenders.
After all, accidentally dropping a pound of dog food on my puppy is one thing, but hacking the dispenser and shooting dog food at Mango is completely unacceptable! Used correctly, these methods will serve us, enable secure digital transformation and maybe help ease the burden on puppies and their owners.
To see how Zscaler is helping its customers reduce business risk, improve user productivity and reduce cost and complexity, visit https://www.zscaler.com/platform/zero-trust-exchange
Sanjit Ganguli is VP Transformation Strategy & Field CTO at Zscaler. Sam Curry is VP, CISO at Zscaler. Nathan Howe is VP Emerging Technology at Zscaler.
This content was originally published here.
About Actiphy and Cybersecurity: As the digital landscape continually evolves, the importance of robust cybersecurity measures cannot be overstated. Actiphy provides a comprehensive suite of solutions designed to address the multifaceted challenges of today’s cybersecurity environment. From data backup to rapid system recovery, our tools are designed with a proactive approach to safeguarding your digital assets. In the context of automation and orchestration, Actiphy’s solutions can seamlessly integrate with your existing systems, enhancing their efficiency and reducing vulnerabilities. Learn more about how Actiphy is championing secure digital transformations by visiting our solutions page.