The notorious Lockbit ransomware group has leaked a trove of data belonging to the leading global aerospace company Boeing, apparently following failed ransom negotiations.
The notorious LockBit ransomware group has struck again, and this time, its victim is aerospace giant Boeing. The ransomware gang infiltrated Boeing’s systems and stole a significant amount of sensitive data.
Timeline of the attack and data leak
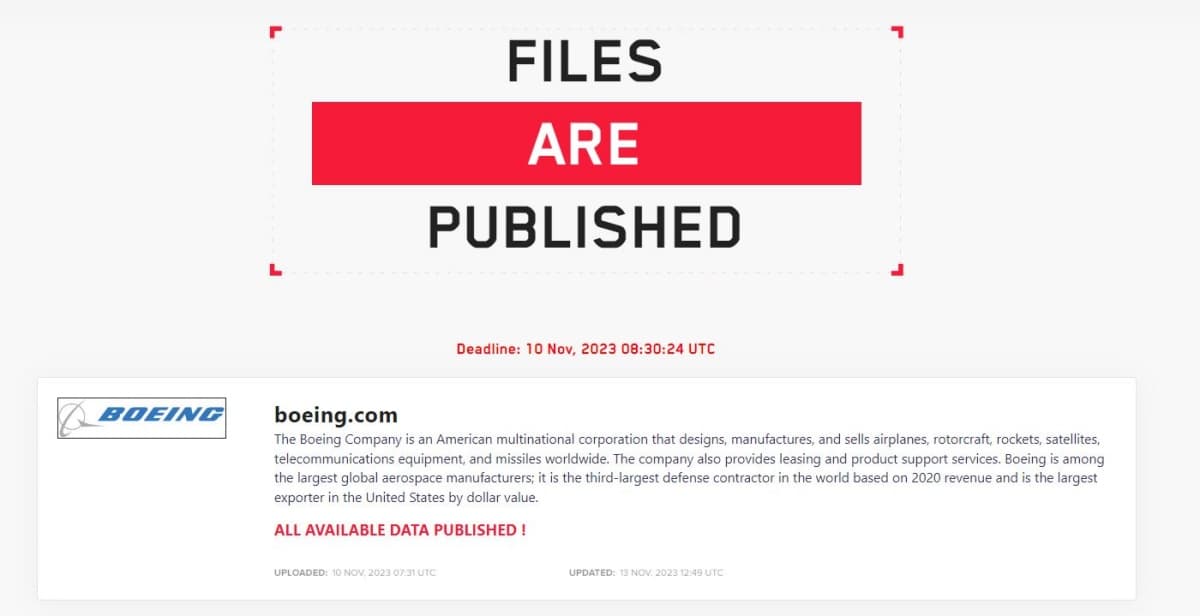
On October 27, 2023, the hackers mentioned Boeing on their data leak website, and gave the firm a 2nd November deadline, revealing to have exfiltrated a tremendous amount of sensitive archive and backup data. The company was given 48 hours to contact LockBit.
On November 2nd, 2023, as reported by Hackread.com, Boeing acknowledged that it suffered a cyberattack but did not confirm whether it was a ransomware attack and if Lockbit’s claims were authentic.
Later, the group removed Boeing from its site, claiming that negotiations had started. Then, the company reappeared on November 7 with another message from LockBit stating that the company ignored warnings.
The hackers then published 4GB of data as a sample, which comprised backup files of different systems featuring an October 22 timestamp. Boeing’s continued silence on the incident prompted LockBit to release all the stolen data on their website on November 10.
This included Boeing’s IT management software’s configuration backups, and auditing/monitoring tools logs. It also included Citrix appliances’ backups, sparking speculation that the hackers might have exploited the Citrix Bleed vulnerability (CVE-2023-4966).
According to MalwareHunterTeam’s assessment, most of the exposed files are associated with a Boeing-owned aviation and aerospace parts manufacturer called Aviall.
Boeing, one of the world’s leading aerospace firms that operate defence systems and commercial aeroplanes, has confirmed the hacking, stating that it is investigating the incident to verify LockBit’s claims and “determine the scope of any potential data breach.”
The company intends to take “appropriate steps” to protect its customers and information. Boeing has also stated that the incident doesn’t threaten aircraft or flight safety.
Boeing’s services website is down currently. This is a developing story, and Hackread will update you about the incident when there’s some clarity about the root cause of the hacking.
The LockBit ransomware gang has been active since 2020 and claimed several high-profile victims, including DXC Technology, Accenture, and the German government, via double extortion. As per CISA’s advisory, since 2020 LockBit targeted 1,700 US firms and made around $91 million in ransom payments.
What Experts Have to Say!
Comparitech’s head of data research, Rebecca Moody, shared an exclusive comment on this incident with Hackread.com, stating that LockBit has emerged as one of the most prevalent ransomware-as-a-service operators this year.
“LockBit has been particularly prevalent this year when it comes to the confirmed ransomware attacks we’ve tracked worldwide. So far this year, we’ve recorded 122 confirmed LockBit attacks,” Rebecca said.
Rebecca further revealed that “In 2022, we recorded 97 LockBit attacks throughout the entire year. The number of confirmed records impacted by these breaches has skyrocketed, too. In 2022, LockBit is confirmed to have stolen 957,438 records across 26 attacks (creating an average of 36,825 records per attack).”
“This year, just over 9.3 million records are confirmed to have been impacted in 20 attacks (465,194). Adding to this are the huge ransom demands being made by the cybercriminals. So far, LockBit has demanded a whopping $196.6 million in ransoms across 15 attacks alone (an average of $13.1 million per case). In 2022, $137.4 million was demanded across 18 cases (an average of $7.63 per case),” she explained.
Nevertheless, while not new to cyberattacks, when it comes to cybersecurity, it is a challenging day for Boeing. It will be crucial to see how the company responds to the situation.
This content was originally published here.