Navigating the Future of Data Protection
Introduction
Welcome back to our ongoing series on the evolving landscape of data protection. I’m Richard Giddey, your navigator through this complex but critical domain. Today, we will dissect the vital relationship between cybersecurity and data protection and why you can’t effectively have one without the other.
The Inseparable Duo: Cybersecurity and Data Protection
Understanding The Bond
In an era of cyber threats like ransomware and data breaches, cybersecurity is not a standalone concept but is deeply interwoven with data protection. Both play essential roles in safeguarding an organisation’s most valuable asset-data.
The Anatomy of a Resilient Infrastructure
Hardware and Software Synergy
The bedrock of a resilient infrastructure lies in the symbiotic relationship between hardware and software. While robust servers and data storage solutions are key, they must be complemented by agile software solutions capable of mitigating real-time security risks. For instance, next-gen antivirus software can detect anomalies that traditional firewalls may overlook.
Layered Security: The Pillars of Defence
Effective security is like a well-designed fortress comprising multiple layers, each serving a specific function. Firewalls may serve as the moat, but intrusion detection systems act as the watchtowers, ever vigilant against new cyber threats. Regular security audits and updates keep the fortress standing tall.
Employee Training: The First Line of Defence
The human element is one of the most overlooked aspects of a resilient infrastructure. No amount of sophisticated hardware or software can compensate for a poorly trained staff susceptible to social engineering attacks.
Bridging the Protection Gap: Backup Strategies
Beyond Traditional Backup
Gone are the days when backup strategies were solely meant for accidental deletions or hardware failures. With the rise of ransomware attacks, a backup is often the last line of defence. Modern backup solutions offer features like real-time monitoring and encryption to ensure your data is retrievable and secure even in a cyberattack.
Keeping an Eye on Regulatory Requirements
In a world where data sovereignty and privacy issues are under intense scrutiny, being aware of and compliant with the current legislation is not optional but mandatory.
Concluding Thoughts
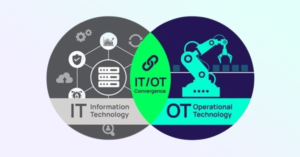
We live in an era where cybersecurity and data protection are converging rapidly…
A Brief Introduction
I am Richard Giddey, the Vice President for the Asia-Pacific region at Actiphy. With a history spanning more than two decades in storage, backup, and data protection, I’ve been involved in the APAC market through various roles, including co-founding the APAC division of StorageCraft and holding key positions at Exabyte Tape.
My Journey and Motivation for this Series
This blog series emanates from my passion for solving real-world data protection challenges and extensive experience in this field. It aims to provide actionable insights and clear guidance to navigate this complex area. I invite you to stay tuned for our next piece, “Modern Data Protection: What to Look for in 2023 and Beyond.”