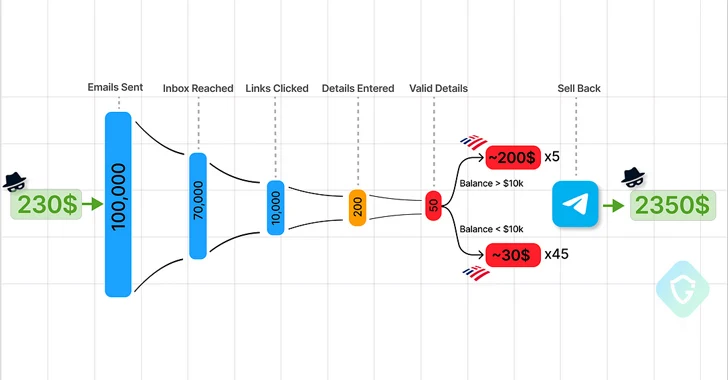
Cybersecurity researchers are calling attention to the “democratization” of the phishing ecosystem owing to the emergence of Telegram as an epicenter for cybercrime, enabling threat actors to mount a mass attack for as little as $230. “This messaging app has transformed into a bustling hub where seasoned cybercriminals and newcomers alike exchange illicit tools and insights creating a dark and well-oiled supply chain of tools and victims’ data,” Guardio Labs researchers Oleg Zaytsev and Nati Tal said in a new report. “Free samples, tutorials, kits, even hackers-for-hire — everything needed to construct a complete end-to-end malicious campaign.” This is not the first time the popular messaging platform has come under the radar for facilitating malicious activities, which are in part driven by its lenient moderation efforts. As a result, what used to be available only on invite-only forums in the dark web is now readily accessible via public channels and groups, thereby opening the doors of cybercrime to aspiring and inexperienced cyber criminals. In April 2023, Kaspersky revealed how phishers create Telegram channels to educate newbies about phishing as well as advertise bots that can automate the process of creating phishing pages for harvesting sensitive information such as login credentials. One such malicious Telegram bot is Telekopye (aka Classiscam), which can craft fraudulent web pages, emails, SMS messages to help threat actors pull off large-scale phishing scams. Guardio said the building blocks to construct a phishing campaign can be readily purchased off Telegram – “some offered at very low prices, and some even for free” – thereby making it possible to set up scam pages via a phishing kit, host the page on a compromised WordPress website via a web shell, and leverage a backdoor mailer to send the email messages. Backdoor mailers, marketed on various Telegram groups, are PHP scripts injected into already infected-but-legitimate websites to send convincing emails using the legitimate domain of the exploited website to bypass spam filters. “This situation highlights a dual responsibility for site owners,” the researchers said. “They must safeguard not only their business interests but also protect against their platforms being used by scammers for hosting phishing operations, sending deceptive emails, and conducting other illicit activities, all unbeknownst to them.” To further increase the likelihood of success of such campaigns, digital marketplaces on Telegram also provide what’s known as “letters,” which are “expertly designed, branded templates” that make the email messages appear as authentic as possible to trick the victims into clicking on the bogus link pointing to the scam page. Telegram is also host to bulk datasets containing valid and relevant email addresses and phone numbers to target. Referred to as “leads,” they are sometimes “enriched” with personal information such as names and physical addresses to maximize the impact. “These leads can be incredibly specific, tailored for any region, niche, demographic, specific company customers, and more,” the researchers said. “Every piece of personal information adds to the effectiveness and credibility of these attacks.” The way these lead lists are prepared can vary from seller to seller. They can be procured either from cybercrime forums that sell data stolen from breached companies or through sketchy websites that urge visitors to complete a fake survey in order to win prizes. Another crucial component of these phishing campaigns is a means to monetize the collected stolen credentials by selling them to other criminal groups in the form of “logs,” netting the threat actors a 10-fold return on their investment based on the number of victims who end up providing valid details on the scam page. “Social media account credentials are sold for as little as a dollar, while banking accounts and credit cards could be sold for hundreds of dollars — depending on their validity and funds,” the researchers said. “Unfortunately, with just a small investment, anyone can start a significant phishing operation, regardless of prior knowledge or connections in the criminal underworld.”
This content was originally published here.