Security researchers discovered a new campaign that distributes a new version of the Xenomorph malware to Android users in the United States, Canada, Spain, Italy, Portugal, and Belgium.
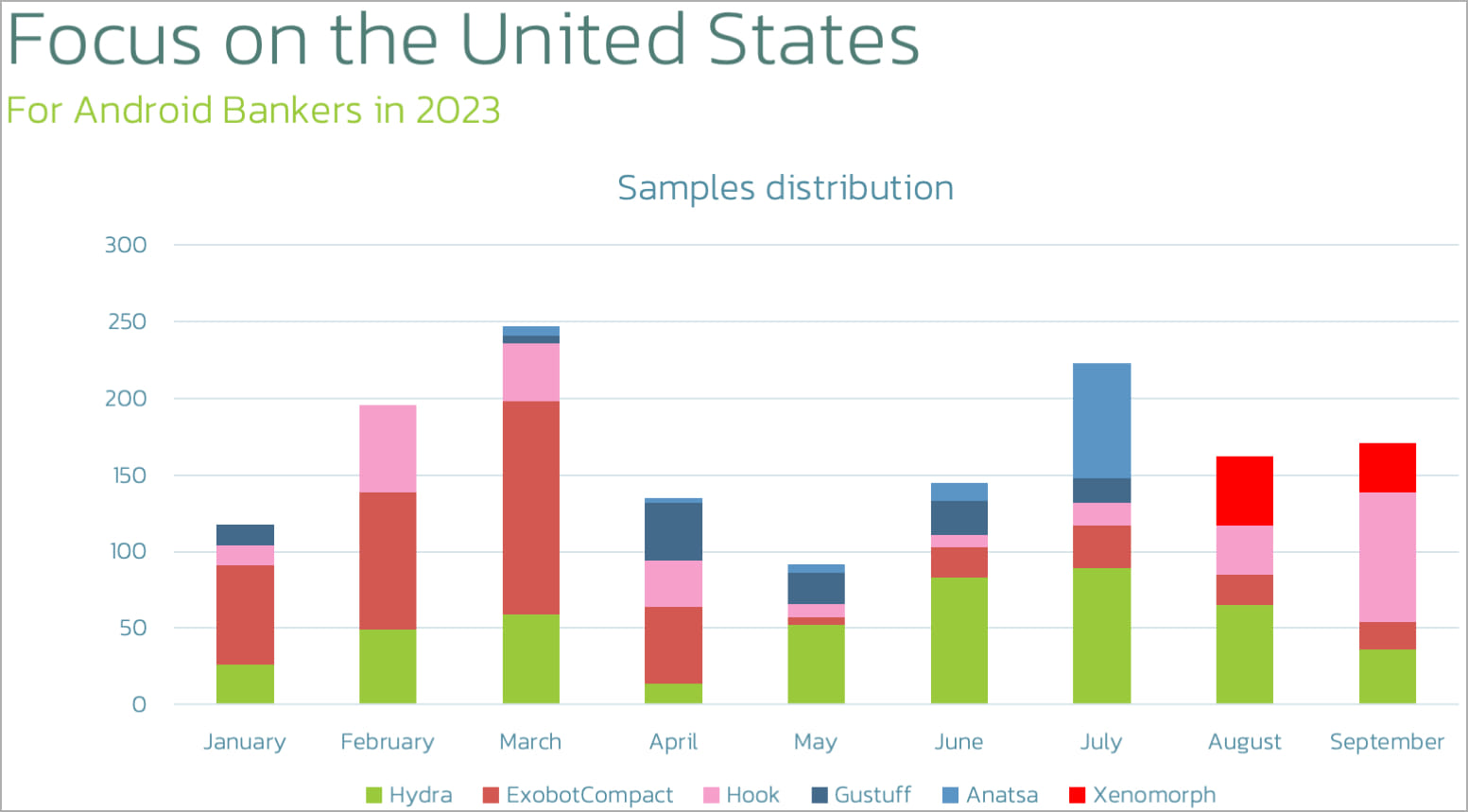
Analysts at cybersecurity company ThreatFabric have been tracking Xenomorph activity since February 2022 and note that the new campaign launched in mid-August.
The latest version of Xenomorph is targeting users of cryptocurrency wallets and various U.S. financial institutions.
Xenomorph background
Xenomorph first appeared in the wild in early 2022, operating as a banking trojan that targeted 56 European banks through screen overlay phishing. It was distributed through Google Play, where it counted over 50,000 installations.
Its authors, “Hadoken Security,” continued development, and in June 2022, they released a rewritten version that made the malware modular and more flexible.
By then, Xenomorph was on Zimperium’s top ten most prolific banking trojans, so it had already achived the “major threat” status.
In August 2022, ThreatFabric reported that Xenomorph was being distributed via a new dropper named “BugDrop,” which bypassed security features in Android 13.
In December 2022, the same analysts reported about a new malware distribution platform dubbed “Zombinder,” which embedded the threat into legitimate Android apps’ APK file.
Most recently, in March 2023, Hadoken released the third major version of Xenomorph, featuring an automated transfer system (ATS) for autonomous on-device transactions, MFA bypass, cookie stealing, and the ability to target over 400 banks.
New campaign
In the latest campaign, the malware operators opted to use phishing pages, luring visitors to update their Chrome browser and trick them into downloading the malicious APK.

The malware continues to use overlays to steal information. However, it has now expanded its targeting scope to include financial institutions from the United States and multiple cryptocurrency apps.
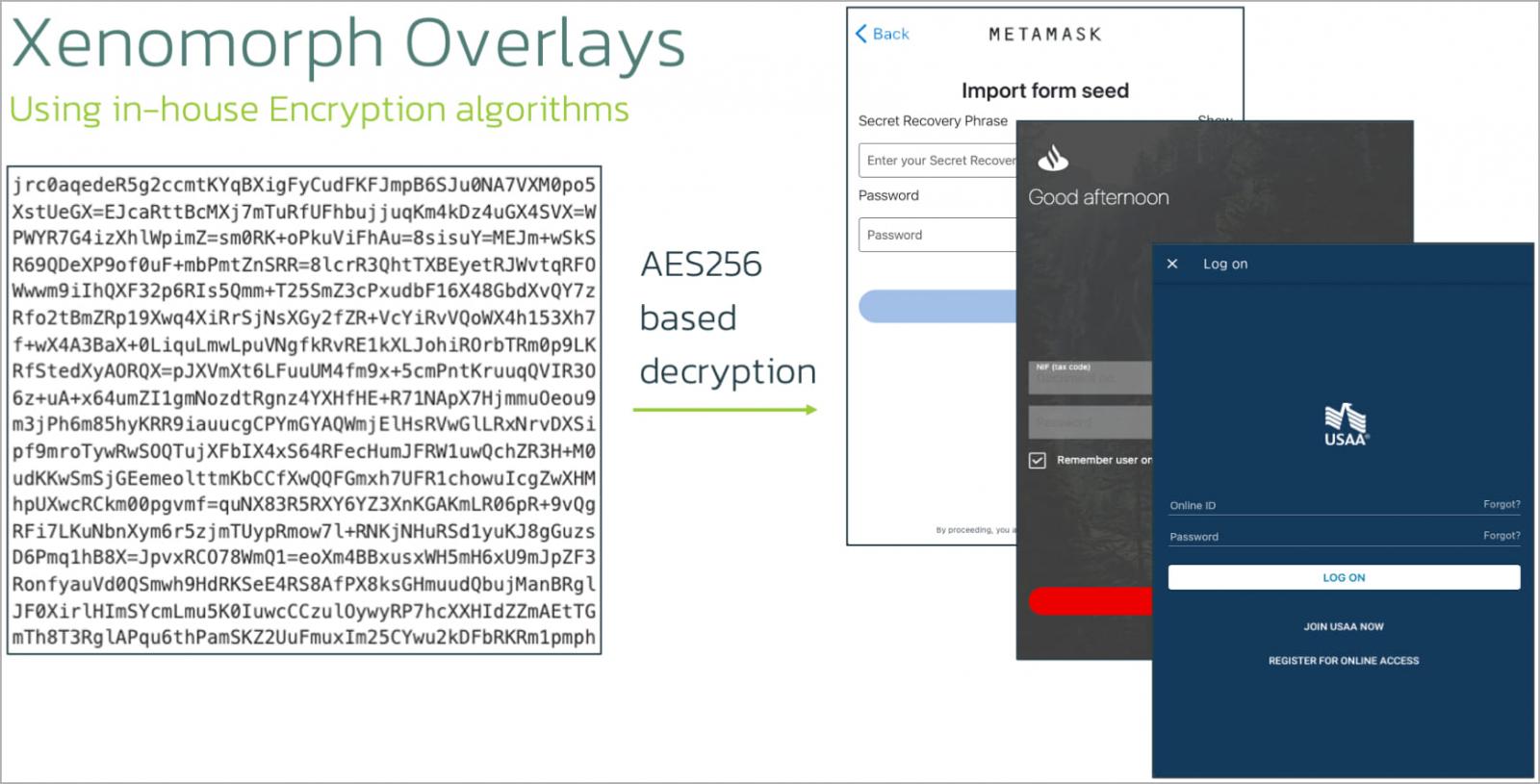
ThreatFabric explains that each Xenomorph sample is loaded with roughly a hundred overlays targeting different sets of banks and crypto apps, depending on the targeted demographic.
Latest version
Although the new Xenomorph samples aren’t vastly different from previous variants, they come with some new features indicating that its authors continue to refine and enhance the malware.
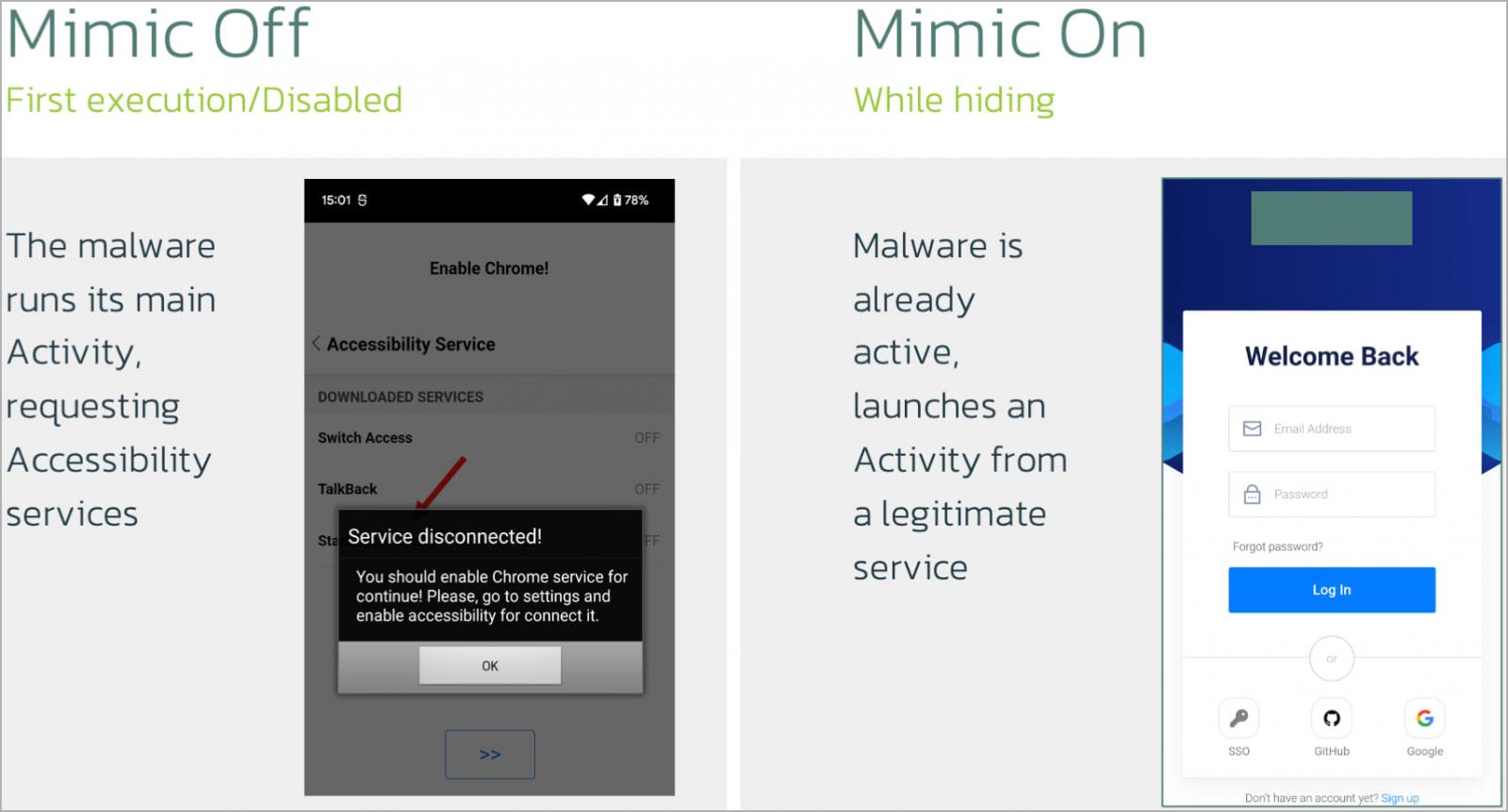
First, a new “mimic” feature can be activated by a corresponding command, giving the malware the capability to act as another application.
Additionally, mimic has a built-in activity named IDLEActivity, which acts as a WebView to display legitimate web content from the context of a trusty process.
This system replaces the need to hide icons from the app launcher post-installation, which is flagged as suspicious behavior by most mobile security tools.
Another new feature is “ClickOnPoint,”, which allows Xenomorph operators to simulate taps at specific screen coordinates.
This allows the operators to move past confirmation screens or perform other simple actions without employing the full ATS module, which might trigger security warnings.
Finally, there’s a new “antisleep” system that prevents the device from switching off its screen by means of an active notification.
This is useful for prolonging the engagement and avoiding interruptions that require re-establishing command and control communications.
Other findings
By taking advantage of weak security measures from the malware operator, ThreatFabric analysts could access their payload hosting infrastructure.
There, they discovered additional malicious payloads, including the Android malware variants Medusa and Cabassous, the Windows information stealers RisePro and LummaC2, and the Private Loader malware loader.
Users should be cautious with prompts on mobile to update their browsers, as those are likely part of malware distribution campaigns.
Xenomorph’s distribution alongside potent Windows malware suggests collaboration between threat actors or the possibility of the Android trojan being sold as Malware-as-a-Service (MaaS).
This content was originally published here.